What is it?
Service Organization Control or SOC for Cybersecurity is a voluntary framework launched by the AICPA to standardize the reporting on the effectiveness of an organization’s cyber risk management controls.
It is a third-party validation of the entity’s cybersecurity risk control program. The program assesses the policies, procedures, and controls of the entity that are tailored to protect information and systems from security incidents, which could undermine the achievement of the entity’s cybersecurity objectives.
The AICPA’s intent is to establish consistent language to present a report on cybersecurity performance and set up a recognized technique for cybersecurity assessments. This report will help stakeholders in acquiring an adequate understanding of the organizations’ security.
Framework
While collaborating with an independent advisor, this framework may take three major courses of action:
- An examination-level attestation engagement.
- A cyber risk appraisal and gap analysis.
- Extensive risk-based cybersecurity design process.
Why is it needed?
A company may have a robust internal cybersecurity risk management program in place. However, the third-party audit is necessary because it:
- Provides the organization with another perspective and facilitates a new eye view of the controls.
- Assesses whether the controls in place are functioning correctly and are relevant for the organization’s cybersecurity program.
- The vast audience for SOC for Cybersecurity makes it beneficial for the entity to conduct this audit program.
- It aids in the more formal and appropriate decision-making process of an organization.
An independent cyber risk appraisal that matches the ordeals of SOC attestation provides a greater level of assurance to management and the board of directors, as well as interested third parties. The attestation can likewise be applied to advise a cyber-liability insurance policy.
Benefits of SOC for cybersecurity
SOC for Cybersecurity generates various benefits for an organization. Some of them are listed below:
- Establish trust and confidence among current and prospective customers.
- Authenticate the risk management framework and manifest the business value.
- Detect and fill the gaps.
- Build an appropriate framework in place.
- Foster internal operational efficiency.
- Magnify transparency and assurance about cybersecurity program effectiveness.
Who reads the report?
It is a general use report mainly designed to address the needs of stakeholders whose decisions are personally affected by the effectiveness of cybersecurity controls of the organization. It may be provided to:
- Management and board members
- Business partners
- Investors
- Analysts
- Industry regulators
- Clients/prospects
This engagement may be carried out for almost any type of organization, regardless of the size or the industry in which it carries out its business. However, these assessments are critically needed in the financial services industry, as it has become a top target of cyber attacks.
SOC for Cybersecurity Report Types
The contents of the report include:
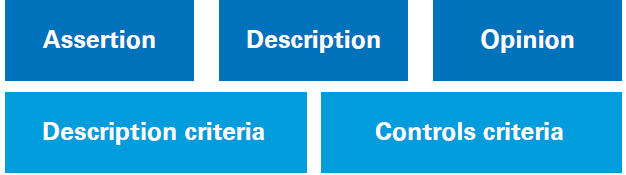
Management’s Assertion: The assertion addressing whether the description is developed in conformity with the description criteria and also that the controls of the entity’s cyber risk are adequate to achieve the entity’s cybersecurity objectives based on the control criterion.
Management’s Description: A explanation of the entity’s cyber risk management program.
The Practitioner’s Opinion: Opinion describing the effectiveness of controls in accomplishing the entity’s cybersecurity objectives.
There are two types of SOC for Cybersecurity Reports:
| Type I | Type II | |
|---|---|---|
| Coverage | Point of time (Specific event) | Period (Specific review period) |
| Assessment | Description of systems Internal controls suitability | Description of systems Internal controls suitability Operating effectiveness of controls |
| Required By | First-time issuers as pre-cursor to Type 2 |
For the Cybersecurity examination, a service organization may choose a design-only SOC. It may adopt this approach if a sufficient length of time has not passed since they have been in operation, or if recently.
Significant changes were made to their cybersecurity risk management program. However, these examinations cannot provide the audience with sufficient information to assess the effectiveness of cybersecurity controls. It only presents the suitability of the design of controls to meet cybersecurity objectives and the cybersecurity risk management program description.
With the evolution of the information security landscape, cybersecurity risks are at the forefront of business issues regarding risk and potential exposure. Despite having a sophisticated cybersecurity risk management program, managing this risk is a challenge.
Organizations must try every possible move to restrain, detect, and mitigate cybersecurity risks. The pressure to show the management of cybersecurity threats and the effectiveness of processes and controls is intensifying. SOC for Cybersecurity can be a valuable tool to meet this challenge. Talk to us today to learn more and get started.





