Many mortgage service providers may find themselves being asked to provide a SOC Report more often in the coming year. Even before the Coronavirus pandemic, financial service companies were being targeted by cyber attacks at an increasing rate. In an effort to increase general security, financial service companies are experiencing growing concern about the security of their service providers in addition to their own security and controls.
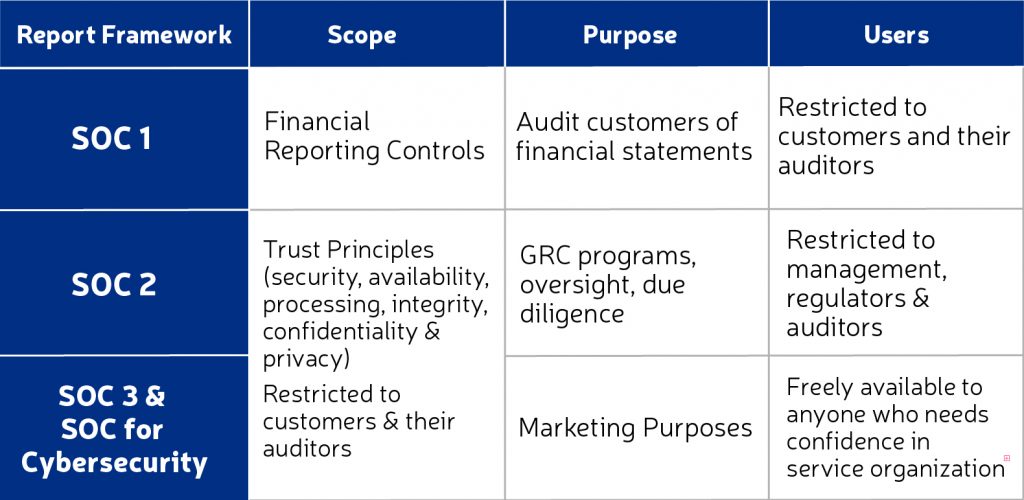
Depending on the needs of your organization, a SOC 1, SOC 2, SOC 3, or SOC for Cybersecurity can help you prove to your customers that you value security, which can affect your mutual clients, employees and financial data. The content and situation for each kind of report is described below.
In addition, management will have to determine whether a Type 1 report (test of control design), or Type 2 report (test of operating effectiveness) is necessary. Typically, a Type 1 report is conducted in year 1 and Type 2 reports each year thereafter.
Generally, the first step in the process is to choose the right type of SOC Audit for your needs.
SOC 1
These reports are appropriate for services that impact financial reporting controls. Service organizations who provide support around mortgage origination, loan servicing, and banking usually need this type of SOC Audit. Your customers will want you to have appropriate controls and financial practices to meet your service agreement, and provide comfort that financial transactions on their behalf will be processed completely, accurately, timely, and consistently. The distribution of this report is restricted to users of the service organization, and their auditors. It cannot be publicly distributed.
SOC 2
These reports are appropriate for service organizations who provide services that do not impact financial reporting, but are relevant to the security, availability, and processing integrity of the systems used to process data, as well as the confidentiality and privacy of the data during processing. A service provider who offers out-sourced cloud based data center would need this type of report. You will be evaluated by the Trusted Services Criteria as prescribed by the AICPA. The distribution of this report is restricted to users of the service organization, and their auditors. It cannot be publicly distributed.
SOC 3
Similar to a SOC 2 report, these reports are appropriate for service organizations whose customers need assurance regarding controls relevant to the security, availability, and processing integrity of the systems used to process data, but do not have the need or knowledge necessary to effectively use a SOC 2 report. In contrast to a SOC 1 or SOC 2 report, these are general use reports that can be publicly distributed.
SOC for Cybersecurity
These reports are appropriate for service organizations who have a need to communicate relevant, useful information about the effectiveness of their cybersecurity risk management program. Like the SOC 3 report, this is a general use report that can be freely distributed.
Your SOC Auditor should spend time explaining the process for each SOC Type before you begin to help you determine what you need to meet the security requirements your customers expect.
Our SOC Audit Team has mortgage-industry experience and is focused on helping mortgage service providers have a great SOC experience. Contact us to lean more or get started.





