Both stories contained within this post are true but identifying facts have been changed to protect those impacted.
Ransomware
According to the 2019 FBI Internet Crime Report, 3.5 billion dollars was estimated to have been lost to different cybercrimes last year, with ransomware steadily increasing as one of the most common and successful cybercrimes. The following example is a real-life cyber-attack that affected a mid-sized firm in 2019.
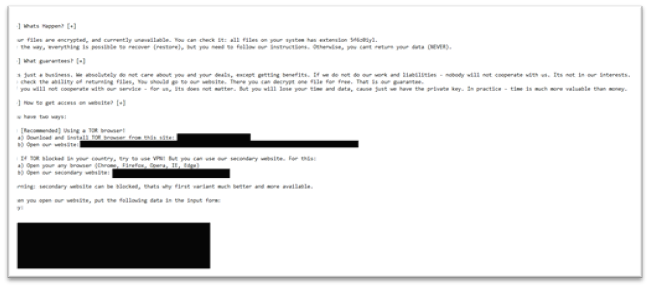
Trapped Files Cry for Help : A mid-sized independent mortgage originator has outsourced a significant portion of their IT needs to a regional managed service provider (MSP). This MSP maintains the firm’s assets by installing a tool that allows patching and remote software deployment, as well as maintaining the Anti-Virus on the workstations. Around 6am on the first Monday following a record month, employees began reporting to the IT department that they were unable to access their files. The IT department quickly noticed during their investigations the presence of oddly named text files in most areas of the network. These text files were the ransom notes with instructions on how to pay the ransom and decrypt the data.
Luckily for this firm, they were doing a trial with an Endpoint Detection and Response (EDR) tool that was able to identify and stop the spread of this ransomware attack to 90% of the firm. During the investigation into what happened and how the malicious software was deployed, it was determined that the outsourced IT provider was the root cause.
The IT provider had an employee account become compromised which provided the malicious actor access to the tool that managed their client’s endpoints. The malicious actor used this tool to deploy the malicious software and created an exclusion within the Anti-Virus to ignore the ransomware. This provided the malicious actor complete unrestricted access to deploy the ransomware to all the lender’s machines. If it was not for the fact that the lender was trialing a new security tool, this attack would most likely have been well over 1 million dollars to remediate.
How to Avoid this: Ransomware can be tricky to protect against the first line of defense should be education for your employees on how to identify risky emails and messages. However technical controls are also a must, consider the use of an EDR tool, as it can go a long way in protection an organization. Additionally, if your firm utilizes outsourced IT providers, consider utilizing a separate organization for security to ensure there is proper segregation between IT and security.
Phishing and Business Email Compromise
Business Email Compromise (BEC) Is the most financially impactful form of cybercrime with thieves taking $12.5 billion dollars between 2013-2018 according to the FBI.
The Haunted Emails No One Remembered Sending: A large organization’s internal IT Department begins receiving alerts from employees that some other employees are sending out spam emails. This IT department believes that one of the organizations employee accounts have been compromised and resets the password on that account. The IT department believes the problem is solved, but a week later another employee notices that they have many messages in their sent folder that the user does not remember sending. The IT department determines that forwarding rules have been set up on several employee accounts and that hundreds of thousands of sensitive emails were sent out containing financial information of clients.
The company hired a forensic team to investigate the incident and determine the size and scope of the problem. The Forensic team found that a phishing email was sent to several hundred employees that contained a PDF of a contract and the body of the email stressed that the recipient’s signature was needed ASAP to get this contract approved. When the individual opened the attachment, it would direct the recipient to a fake Microsoft login page. Only 1 of the several hundred employees who received fell for this phishing email and entered their credentials. From there, the malicious actor utilized the compromised account to continue to send the same phishing email, but now that the email was coming from inside the organization more employees were tricked.
By the end of this investigation nearly 100,000 unique individual financial records were stolen and the forensic investigation cost upwards of $250,000 to conduct. This incident is still ongoing, but there are significant penalties expected for failure to protect consumer data. All of this was caused by the failure of 1 employee out of hundreds who failed to identify a phishing email.
How to Avoid this: This entire incident could have been prevented if external auto-forwarding was disabled globally for the organization, along with specific training for employees focused on how to identify phishing emails. Additionally, it is considered best practice to routinely test employees with simulated phishing emails as a means of getting them in the habit of identifying and reporting phishing emails.
Our Technology Solutions team can help you keep your cybersecurity practices ahead of the game, while you do what you do best: keep your company running through whatever comes in 2021 and beyond. Talk to us today to learn more about our comprehensive cybersecurity services.





